1. EC2 인스턴스 생성
주의) EC2에 도메인을 연결시키지 않으면 Certbot이 정상적으로 작동하지 않는다.
EC2 인스턴스 서비스에 접속하여 리전(Region)을 아시아 태평양 (서울)로 선택
"인스턴스 시작" 버튼 클릭
- 이름 : test-server
- 애플리케이션 및 OS 이미지(Amazon Machine Image) : Ubuntu Server 24.04 LTS (HVM), SSD Volume Type
- 인스턴스 유형 : t2.micro
- 키 페어
이름 : test-server-key-pair
키 페어 유형 : RSA
프라이빗 키 파일 형식 : .pem
- 네트워크 설정 - 방화벽(보안 그룹)
보안 그룹 이름 : test-server-security-group
설명 : test-server-security-group created 2025-12-31T02:27:00.089Z
인바운드 보안 그룹 규칙)
보안 그룹 규칙 1 (TCP, 22, 0.0.0.0/0)
유형 : ssh
프로토콜 : TCP
포트 범위 : 22
소스 유형 : 위치 무관
보안 그룹 규칙 2 (TCP, 80, 0.0.0.0/0)
유형 : HTTP
프로토콜 : TCP
포트 범위 : 80
소스 유형 : 위치 무관
보안 그룹 규칙 3 (TCP, 443, 0.0.0.0/0)
유형 : HTTPS
프로토콜 : TCP
포트 범위 : 443
소스 유형 : 위치 무관
보안 그룹 규칙 4 (TCP, 3000, 0.0.0.0/0)
유형 : 사용자 지정 TCP
프로토콜 : TCP
포트 범위 : 3000
소스 유형 : 위치 무관
- 스토리지 구성
크기(GiB) : 8
볼륨 유형 : gp2
"인스턴스 시작" 버튼 클릭
2. 탄력적 IP 주소 생성
네트워크 및 보안 > 탄력적 IP 메뉴 선택
"탄력적 IP 주소 할당" 버튼 클릭
탄력적 IP 주소 할당)
퍼블릭 IPv4 주소 풀 : Amazon의 IPv4 주소 풀 선택 (기본 설정)
"할당" 버튼 클릭
할당된 IPv4 주소 선택 후, 작업 > 탄력적 IP 주소 연결 클릭
생성한 EC2 인스턴스 선택 후 "연결" 버튼 클릭
인스턴스 > 인스턴스 메뉴에서 생성한 EC2 인스턴스 요약의 퍼블릭 IPv4 주소를 보면 탄력적 IP 주소 연결이 잘 된 것을 확인할 수 있다.
3. EC2 인스턴스 연결 후 Express 서버 배포 / Express 서버 실행 포트를 3000번으로 설정
생성한 EC2 인스턴스에 접속하여 Express 서버를 배포한다.
- Ubuntu
ubuntu@ip-172-31-3-3:~$ sudo su
root@ip-172-31-3-3:/home/ubuntu# apt-get update && /
apt-get install -y ca-certificates curl gnupg && /
mkdir -p /etc/apt/keyrings && /
curl -fsSL https://deb.nodesource.com/gpgkey/nodesource-repo.gpg.key | sudo gpg --dearmor -o /etc/apt/keyrings/nodesource.gpg && /
NODE_MAJOR=20 && /
echo "deb [signed-by=/etc/apt/keyrings/nodesource.gpg] https://deb.nodesource.com/node_$NODE_MAJOR.x nodistro main" | sudo tee /etc/apt/sources.list.d/nodesource.list && /
apt-get update && /
apt-get install nodejs -y
Hit:1 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble InRelease
Get:2 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates InRelease [126 kB]
Get:3 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports InRelease [126 kB]
Get:4 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble/universe amd64 Packages [15.0 MB]
Get:5 http://security.ubuntu.com/ubuntu noble-security InRelease [126 kB]
Get:6 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble/universe Translation-en [5982 kB]
Get:7 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble/universe amd64 Components [3871 kB]
Get:8 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble/universe amd64 c-n-f Metadata [301 kB]
Get:9 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble/multiverse amd64 Packages [269 kB]
Get:10 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble/multiverse Translation-en [118 kB]
Get:11 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble/multiverse amd64 Components [35.0 kB]
Get:12 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble/multiverse amd64 c-n-f Metadata [8328 B]
Get:13 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/main amd64 Packages [1684 kB]
Get:14 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/main Translation-en [311 kB]
Get:15 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/main amd64 Components [175 kB]
Get:16 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/main amd64 c-n-f Metadata [15.8 kB]
Get:17 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/universe amd64 Packages [1506 kB]
Get:18 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/universe Translation-en [306 kB]
Get:19 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/universe amd64 Components [378 kB]
Get:20 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/universe amd64 c-n-f Metadata [31.4 kB]
Get:21 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/restricted amd64 Packages [2413 kB]
Get:22 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/restricted Translation-en [550 kB]
Get:23 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/restricted amd64 Components [212 B]
Get:24 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/restricted amd64 c-n-f Metadata [516 B]
Get:25 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/multiverse amd64 Packages [30.3 kB]
Get:26 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/multiverse Translation-en [6048 B]
Get:27 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/multiverse amd64 Components [940 B]
Get:28 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/multiverse amd64 c-n-f Metadata [488 B]
Get:29 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/main amd64 Packages [40.4 kB]
Get:30 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/main Translation-en [9208 B]
Get:31 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/main amd64 Components [7300 B]
Get:32 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/main amd64 c-n-f Metadata [368 B]
Get:33 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/universe amd64 Packages [29.5 kB]
Get:34 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/universe Translation-en [17.9 kB]
Get:35 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/universe amd64 Components [10.5 kB]
Get:36 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/universe amd64 c-n-f Metadata [1444 B]
Get:37 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/restricted amd64 Components [216 B]
Get:38 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/restricted amd64 c-n-f Metadata [116 B]
Get:39 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/multiverse amd64 Components [212 B]
Get:40 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/multiverse amd64 c-n-f Metadata [116 B]
Get:41 http://security.ubuntu.com/ubuntu noble-security/main amd64 Packages [1391 kB]
Get:42 http://security.ubuntu.com/ubuntu noble-security/main Translation-en [225 kB]
Get:43 http://security.ubuntu.com/ubuntu noble-security/main amd64 Components [21.5 kB]
Get:44 http://security.ubuntu.com/ubuntu noble-security/main amd64 c-n-f Metadata [9504 B]
Get:45 http://security.ubuntu.com/ubuntu noble-security/universe amd64 Packages [916 kB]
Get:46 http://security.ubuntu.com/ubuntu noble-security/universe Translation-en [207 kB]
Get:47 http://security.ubuntu.com/ubuntu noble-security/universe amd64 Components [71.4 kB]
Get:48 http://security.ubuntu.com/ubuntu noble-security/universe amd64 c-n-f Metadata [19.4 kB]
Get:49 http://security.ubuntu.com/ubuntu noble-security/restricted amd64 Packages [2286 kB]
Get:50 http://security.ubuntu.com/ubuntu noble-security/restricted Translation-en [523 kB]
Get:51 http://security.ubuntu.com/ubuntu noble-security/restricted amd64 Components [212 B]
Get:52 http://security.ubuntu.com/ubuntu noble-security/multiverse amd64 Packages [27.4 kB]
Get:53 http://security.ubuntu.com/ubuntu noble-security/multiverse Translation-en [5956 B]
Get:54 http://security.ubuntu.com/ubuntu noble-security/multiverse amd64 Components [212 B]
Get:55 http://security.ubuntu.com/ubuntu noble-security/multiverse amd64 c-n-f Metadata [384 B]
Fetched 39.2 MB in 16s (2510 kB/s)
Reading package lists... Done
bash: /: Is a directory
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
ca-certificates is already the newest version (20240203).
ca-certificates set to manually installed.
curl is already the newest version (8.5.0-2ubuntu10.6).
curl set to manually installed.
gnupg is already the newest version (2.4.4-2ubuntu17.3).
gnupg set to manually installed.
0 upgraded, 0 newly installed, 0 to remove and 68 not upgraded.
bash: /: Is a directory
bash: /: Is a directory
bash: /: Is a directory
bash: /: Is a directory
deb [signed-by=/etc/apt/keyrings/nodesource.gpg] https://deb.nodesource.com/node_20.x nodistro main
bash: /: Is a directory
Hit:1 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble InRelease
Hit:2 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates InRelease
Hit:3 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports InRelease
Get:4 https://deb.nodesource.com/node_20.x nodistro InRelease [12.1 kB]
Hit:5 http://security.ubuntu.com/ubuntu noble-security InRelease
Get:6 https://deb.nodesource.com/node_20.x nodistro/main amd64 Packages [13.2 kB]
Fetched 25.3 kB in 1s (35.3 kB/s)
Reading package lists... Done
bash: /: Is a directory
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
The following NEW packages will be installed:
nodejs
0 upgraded, 1 newly installed, 0 to remove and 68 not upgraded.
Need to get 32.0 MB of archives.
After this operation, 197 MB of additional disk space will be used.
Get:1 https://deb.nodesource.com/node_20.x nodistro/main amd64 nodejs amd64 20.19.6-1nodesource1 [32.0 MB]
Fetched 32.0 MB in 1s (46.1 MB/s)
Selecting previously unselected package nodejs.
(Reading database ... 71735 files and directories currently installed.)
Preparing to unpack .../nodejs_20.19.6-1nodesource1_amd64.deb ...
Unpacking nodejs (20.19.6-1nodesource1) ...
Setting up nodejs (20.19.6-1nodesource1) ...
Processing triggers for man-db (2.12.0-4build2) ...
Scanning processes...
Scanning linux images...
Running kernel seems to be up-to-date.
No services need to be restarted.
No containers need to be restarted.
No user sessions are running outdated binaries.
No VM guests are running outdated hypervisor (qemu) binaries on this host.
root@ip-172-31-3-3:/home/ubuntu# node -v
v20.19.6
root@ip-172-31-3-3:/home/ubuntu# git clone https://github.com/JSCODE-EDU/ec2-express-sample
Cloning into 'ec2-express-sample'...
remote: Enumerating objects: 6, done.
remote: Counting objects: 100% (6/6), done.
remote: Compressing objects: 100% (5/5), done.
remote: Total 6 (delta 0), reused 6 (delta 0), pack-reused 0 (from 0)
Receiving objects: 100% (6/6), 7.60 KiB | 1.90 MiB/s, done.
root@ip-172-31-3-3:/home/ubuntu# cd ec2-express-sample
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# npm i
added 63 packages, and audited 64 packages in 3s
12 packages are looking for funding
run `npm fund` for details
7 vulnerabilities (3 low, 4 high)
To address all issues, run:
npm audit fix
Run `npm audit` for details.
npm notice
npm notice New major version of npm available! 10.8.2 -> 11.7.0
npm notice Changelog: https://github.com/npm/cli/releases/tag/v11.7.0
npm notice To update run: npm install -g npm@11.7.0
npm notice
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# vi .env
- Ubuntu Vim
DATABASE_NAME=my_database
~
~
~
~
:wq
- Ubuntu
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# ls
app.js node_modules package-lock.json package.json
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# vi app.js
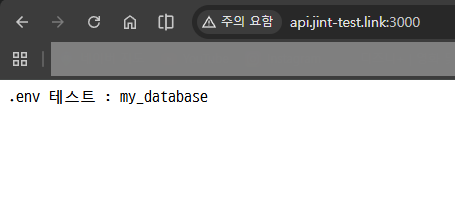
Nginx를 80번 포트에서 실행시킬 것이기 때문에 Express 서버는 3000번에서 띄워준다.
EC2 인스턴스 생성시, 테스트를 위해 보안 그룹에서 3000번 포트를 추가적으로 열어두었다.
- Ubuntu Vim
require('dotenv').config();
const express = require('express');
const app = express();
const port = 3000;
app.get('/', (req, res) => {
res.send(`.env 테스트 : ${process.env.DATABASE_NAME}`);
})
app.listen(port, () => {
console.log(`Example app listening on port ${port}`)
})
~
~
~
~
:wq
- Ubuntu
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# sudo npm i -g pm2
added 133 packages in 10s
13 packages are looking for funding
run `npm fund` for details
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# sudo pm2 start app.js
-------------
__/\\\\\\\\\\\\\____/\\\\____________/\\\\____/\\\\\\\\\_____
_\/\\\/////////\\\_\/\\\\\\________/\\\\\\__/\\\///////\\\___
_\/\\\_______\/\\\_\/\\\//\\\____/\\\//\\\_\///______\//\\\__
_\/\\\\\\\\\\\\\/__\/\\\\///\\\/\\\/_\/\\\___________/\\\/___
_\/\\\/////////____\/\\\__\///\\\/___\/\\\________/\\\//_____
_\/\\\_____________\/\\\____\///_____\/\\\_____/\\\//________
_\/\\\_____________\/\\\_____________\/\\\___/\\\/___________
_\/\\\_____________\/\\\_____________\/\\\__/\\\\\\\\\\\\\\\_
_\///______________\///______________\///__\///////////////__
Runtime Edition
PM2 is a Production Process Manager for Node.js applications
with a built-in Load Balancer.
Start and Daemonize any application:
$ pm2 start app.js
Load Balance 4 instances of api.js:
$ pm2 start api.js -i 4
Monitor in production:
$ pm2 monitor
Make pm2 auto-boot at server restart:
$ pm2 startup
To go further checkout:
http://pm2.io/
-------------
[PM2] Spawning PM2 daemon with pm2_home=/root/.pm2
[PM2] PM2 Successfully daemonized
[PM2] Starting /home/ubuntu/ec2-express-sample/app.js in fork_mode (1 instance)
[PM2] Done.
┌────┬────────┬─────────────┬─────────┬─────────┬──────────┬────────┬──────┬───────────┬──────────┬──────────┬──────────┬──────────┐
│ id │ name │ namespace │ version │ mode │ pid │ uptime │ ↺ │ status │ cpu │ mem │ user │ watching │
├────┼────────┼─────────────┼─────────┼─────────┼──────────┼────────┼──────┼───────────┼──────────┼──────────┼──────────┼──────────┤
│ 0 │ app │ default │ 1.0.0 │ fork │ 2292 │ 0s │ 0 │ online │ 0% │ 29.0mb │ root │ disabled │
└────┴────────┴─────────────┴─────────┴─────────┴──────────┴────────┴──────┴───────────┴──────────┴──────────┴──────────┴──────────┘
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# pm2 list
┌────┬────────┬─────────────┬─────────┬─────────┬──────────┬────────┬──────┬───────────┬──────────┬──────────┬──────────┬──────────┐
│ id │ name │ namespace │ version │ mode │ pid │ uptime │ ↺ │ status │ cpu │ mem │ user │ watching │
├────┼────────┼─────────────┼─────────┼─────────┼──────────┼────────┼──────┼───────────┼──────────┼──────────┼──────────┼──────────┤
│ 0 │ app │ default │ 1.0.0 │ fork │ 2292 │ 20s │ 0 │ online │ 0% │ 51.8mb │ root │ disabled │
└────┴────────┴─────────────┴─────────┴─────────┴──────────┴────────┴──────┴───────────┴──────────┴──────────┴──────────┴──────────┘
확인을 위해 브라우저에서 IP와 포트로 서버에 접속한다.

실행된 서버 종료
- Ubuntu
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# ps aux | grep pm2
root 2281 0.1 5.5 1026616 54372 ? Ssl 03:02 0:00 PM2 v6.0.14: God Daemon (/root/.pm2)
root 2322 0.0 0.2 7076 2076 pts/1 S+ 03:08 0:00 grep --color=auto pm2
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# kill 2281
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# ps aux | grep pm2
root 2325 0.0 0.2 7076 2076 pts/1 S+ 03:08 0:00 grep --color=auto pm2
4. 도메인 적용
Route 53 서비스에 접속하여 호스팅 영역 메뉴 접속
등록된 도메인 클릭하여 호스팅 영역 세부 정보 접속하여 "레코드 생성" 버튼 클릭
- 레코드 이름 : api.jint-test.link
- 레코드 유형 : A - IPv4 주소 및 일부 AWS 리소스로 트래픽 라우팅
- 값 : 43.203.21.221 (IPv4 주소)
"레코드 생성" 버튼 클릭
확인을 위해 브라우저에서 도메인으로 서버에 접속한다.
-> 사전 환경 세팅 끝
5. Nginx 설치
- Ubuntu
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# sudo apt update
Hit:1 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble InRelease
Get:2 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates InRelease [126 kB]
Get:3 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports InRelease [126 kB]
Hit:4 https://deb.nodesource.com/node_20.x nodistro InRelease
Get:5 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/main amd64 Components [175 kB]
Get:6 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/universe amd64 Components [377 kB]
Get:7 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/restricted amd64 Components [212 B]
Get:8 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/multiverse amd64 Components [940 B]
Hit:9 http://security.ubuntu.com/ubuntu noble-security InRelease
Get:10 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/main amd64 Components [7312 B]
Get:11 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/universe amd64 Components [10.5 kB]
Get:12 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/restricted amd64 Components [216 B]
Get:13 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-backports/multiverse amd64 Components [212 B]
Fetched 824 kB in 1s (853 kB/s)
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
68 packages can be upgraded. Run 'apt list --upgradable' to see them.
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# sudo apt install nginx
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
The following additional packages will be installed:
nginx-common
Suggested packages:
fcgiwrap nginx-doc ssl-cert
The following NEW packages will be installed:
nginx nginx-common
0 upgraded, 2 newly installed, 0 to remove and 68 not upgraded.
Need to get 564 kB of archives.
After this operation, 1596 kB of additional disk space will be used.
Do you want to continue? [Y/n] Y
Get:1 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/main amd64 nginx-common all 1.24.0-2ubuntu7.5 [43.4 kB]
Get:2 http://ap-northeast-2.ec2.archive.ubuntu.com/ubuntu noble-updates/main amd64 nginx amd64 1.24.0-2ubuntu7.5 [520 kB]
Fetched 564 kB in 0s (18.4 MB/s)
Preconfiguring packages ...
Selecting previously unselected package nginx-common.
(Reading database ... 77098 files and directories currently installed.)
Preparing to unpack .../nginx-common_1.24.0-2ubuntu7.5_all.deb ...
Unpacking nginx-common (1.24.0-2ubuntu7.5) ...
Selecting previously unselected package nginx.
Preparing to unpack .../nginx_1.24.0-2ubuntu7.5_amd64.deb ...
Unpacking nginx (1.24.0-2ubuntu7.5) ...
Setting up nginx-common (1.24.0-2ubuntu7.5) ...
Created symlink /etc/systemd/system/multi-user.target.wants/nginx.service → /usr/lib/systemd/system/nginx.service.
Setting up nginx (1.24.0-2ubuntu7.5) ...
* Upgrading binary nginx [ OK ]
Processing triggers for man-db (2.12.0-4build2) ...
Processing triggers for ufw (0.36.2-6) ...
Scanning processes...
Scanning linux images...
Running kernel seems to be up-to-date.
No services need to be restarted.
No containers need to be restarted.
No user sessions are running outdated binaries.
No VM guests are running outdated hypervisor (qemu) binaries on this host.
6. Nginx 설치 확인
1) 리눅스 명령어로 확인
- Ubuntu
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# sudo service nginx status
● nginx.service - A high performance web server and a reverse proxy server
Loaded: loaded (/usr/lib/systemd/system/nginx.service; enabled; preset: enabled)
Active: active (running) since Wed 2025-12-31 04:40:03 UTC; 1min 46s ago
Docs: man:nginx(8)
Process: 3052 ExecStartPre=/usr/sbin/nginx -t -q -g daemon on; master_process on; (code=exited, status=0/SUCCESS)
Process: 3053 ExecStart=/usr/sbin/nginx -g daemon on; master_process on; (code=exited, status=0/SUCCESS)
Main PID: 3082 (nginx)
Tasks: 2 (limit: 1121)
Memory: 1.7M (peak: 3.7M)
CPU: 20ms
CGroup: /system.slice/nginx.service
├─3082 "nginx: master process /usr/sbin/nginx -g daemon on; master_process on;"
└─3084 "nginx: worker process"
Dec 31 04:40:03 ip-172-31-3-3 systemd[1]: Starting nginx.service - A high performance web server and a reverse proxy server...
Dec 31 04:40:03 ip-172-31-3-3 systemd[1]: Started nginx.service - A high performance web server and a reverse proxy server.
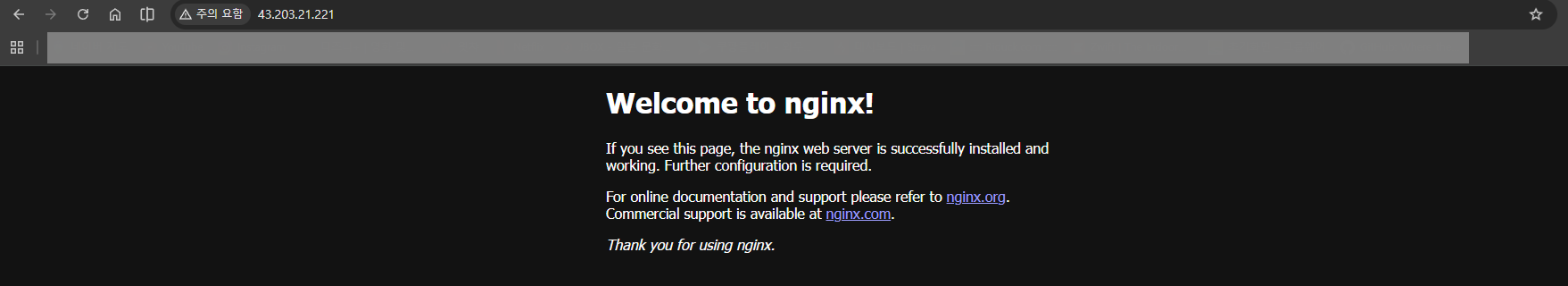
2) EC2 IP로 접속해서 확인
확인을 위해 브라우저에서 IP로 서버에 접속한다.
7. Certbot 설치
SSL 인증서를 발급 받아주는 Certbot을 설치한다.
- Ubuntu
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# sudo snap install --classic certbot
certbot 5.2.2 from Certbot Project (certbot-eff✓) installed
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# sudo ln -s /snap/bin/certbot /usr/bin/certbot
8. SSL 인증서 발급
주의) 반드시 해당 EC2에 도메인을 연결한 뒤에 명령어를 쳐야 정상 작동한다.
- Ubuntu
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# sudo certbot --nginx -d api.jint-test.link
Saving debug log to /var/log/letsencrypt/letsencrypt.log
Enter email address or hit Enter to skip.
(Enter 'c' to cancel): stbhg5@gmail.com
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Please read the Terms of Service at:
https://letsencrypt.org/documents/LE-SA-v1.6-August-18-2025.pdf
You must agree in order to register with the ACME server. Do you agree?
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
(Y)es/(N)o: Y
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Would you be willing, once your first certificate is successfully issued, to
share your email address with the Electronic Frontier Foundation, a founding
partner of the Let's Encrypt project and the non-profit organization that
develops Certbot? We'd like to send you email about our work encrypting the web,
EFF news, campaigns, and ways to support digital freedom.
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
(Y)es/(N)o: Y
Account registered.
Requesting a certificate for api.jint-test.link
Successfully received certificate.
Certificate is saved at: /etc/letsencrypt/live/api.jint-test.link/fullchain.pem
Key is saved at: /etc/letsencrypt/live/api.jint-test.link/privkey.pem
This certificate expires on 2026-03-31.
These files will be updated when the certificate renews.
Certbot has set up a scheduled task to automatically renew this certificate in the background.
Deploying certificate
Successfully deployed certificate for api.jint-test.link to /etc/nginx/sites-enabled/default
Congratulations! You have successfully enabled HTTPS on https://api.jint-test.link
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
If you like Certbot, please consider supporting our work by:
* Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate
* Donating to EFF: https://eff.org/donate-le
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
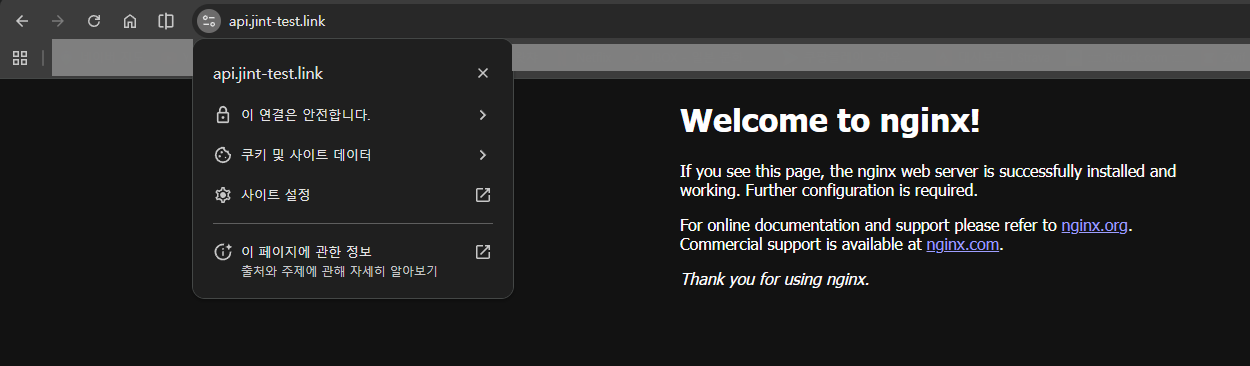
확인을 위해 브라우저에서 HTTPS 도메인으로 서버에 접속한다.
9. 리버스 프록시 설정
80번 포트에는 HTTPS가 적용되었지만 3000번 포트에는 적용되지 않았다.
- Ubuntu
root@ip-172-31-3-3:/home/ubuntu/ec2-express-sample# cd /etc/nginx/sites-available
root@ip-172-31-3-3:/etc/nginx/sites-available# ls
default
root@ip-172-31-3-3:/etc/nginx/sites-available# vi default
- Ubuntu Vim
...
server {
# SSL configuration
#
# listen 443 ssl default_server;
# listen [::]:443 ssl default_server;
#
# Note: You should disable gzip for SSL traffic.
# See: https://bugs.debian.org/773332
#
# Read up on ssl_ciphers to ensure a secure configuration.
# See: https://bugs.debian.org/765782
#
# Self signed certs generated by the ssl-cert package
# Don't use them in a production server!
#
# include snippets/snakeoil.conf;
root /var/www/html;
# Add index.php to the list if you are using PHP
index index.html index.htm index.nginx-debian.html;
server_name api.jint-test.link; # managed by Certbot
location / {
# First attempt to serve request as file, then
# as directory, then fall back to displaying a 404.
# try_files $uri $uri/ =404;
proxy_pass http://localhost:3000/;
}
# pass PHP scripts to FastCGI server
#
#location ~ \.php$ {
:wq
api.jint-test.link 도메인에 요청이 들어오면, http://localhost:3000 서버의 트래픽으로 전달 및 연결하겠다는 의미이다.
80번 포트로 요청이 들어오면 3000번 포트로 이어서 연결시켜 주겠다는 리버스 프록시를 설정했다.
- Ubuntu
root@ip-172-31-3-3:/etc/nginx/sites-available# sudo service nginx restart
설정 적용을 위해 Nginx를 재시작한다.
10. 백엔드 서버 HTTPS 적용 확인
확인을 위해 브라우저에서 HTTPS 도메인으로 서버에 접속한다.
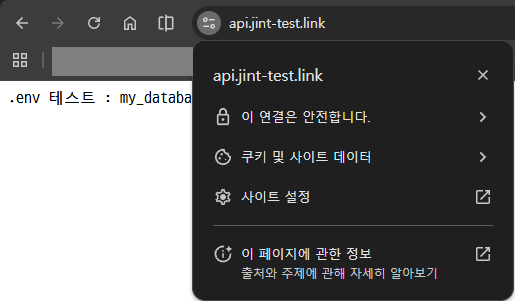
ELB에 대한 비용 및 세팅없이 EC2 인스턴스 안에서만 백엔드 서버 배포, 도메인 적용, HTTPS 적용을 했다.
참고문서1 : https://ubuntu.com/tutorials/install-and-configure-nginx#3-creating-our-own-website
Install and configure Nginx | Ubuntu
Ubuntu is an open source software operating system that runs from the desktop, to the cloud, to all your internet connected things.
ubuntu.com
참고문서2 : https://certbot.eff.org/instructions?ws=nginx&os=ubuntufocal
Certbot Instructions
Certbot Instructions
certbot.eff.org
비전공자도 이해할 수 있는 AWS 입문/실전| JSCODE 박재성 - 인프런 강의
현재 평점 4.9점 수강생 2,868명인 강의를 만나보세요. 비전공자 입장에서도 쉽게 이해할 수 있고, 실전에서 바로 적용 가능한 AWS 입문 강의를 만들어봤습니다! EC2를 활용한 백엔드 API 서버 배포, R
www.inflearn.com
'강의 실습 > 비전공자도 이해할 수 있는 AWS 입문 실전' 카테고리의 다른 글
| RDS를 활용한 아키텍처 구성 (1) | 2026.01.01 |
|---|---|
| RDS란? / RDS를 왜 사용하는걸까? / 현업에서의 RDS (0) | 2026.01.01 |
| [보충 강의] HTTPS 연결 시 ELB vs Nginx, Certbot (0) | 2025.12.30 |
| 비용 나가지 않게 ELB 깔끔하게 종료하기 (0) | 2025.12.30 |
| [실습] 6. ELB에 HTTPS 설정하기 (0) | 2025.12.30 |


댓글